Single Sign-On: Generic SAML
Moesif provides a single sign-on integration with SAML identity providers.
In order to set up SSO:
- You must be able to configure your identity provider
- You must be on a Moesif enterprise plan
Benefits of SSO
- Improve security and regulatory compliance
- Reduce IT costs through auto-provision and de-provisioning
- Enforce policies like Multi-Factor Authentication (MFA), Password Reset, etc
- Improve usability for employees
How SSO works
Moesif supports both identity-provider (IdP) initiated and service-provider (SP) initiated single sign-on. When IdP initiated, a user logs in through your IdP’s app directory. When SP initiated, a user logs in by entering their employee email on Moesif’s website. Because their email domain has SSO enabled, they will be redirected to your organization’s single sign-on page. Once enabled, team management and role-based access control (RBAC) is handled by your identity provider rather than within the Moesif application.
Home Realm Discovery
Moesif’s SSO implementation supports Home Realm Discovery. This means SSO is enforced for your entire company domain even if a new employee is not yet added to your Moesif organization. This ensures employees cannot bypass SSO such as by entering a username/password. It also reduces your IT burden as employees never have to decide on what type of login they should use as redirect is automatic as soon as they enter their email.
Enterprise Single Sign-On is available only on enterprise plans
How create a SAML app using Okta
This guide shows how to set up a generic SAML app with a generic SAML identity provider. If Moesif already has an integration for your provider, we recommend leveraging that instead. If we don’t have a provider specific integration, we recommend OIDC over SAML.
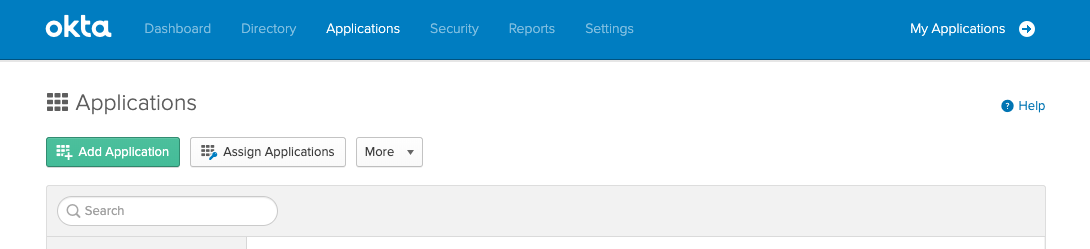
1. Go to Applications within the Okta admin dashboard
Click the Add Application button
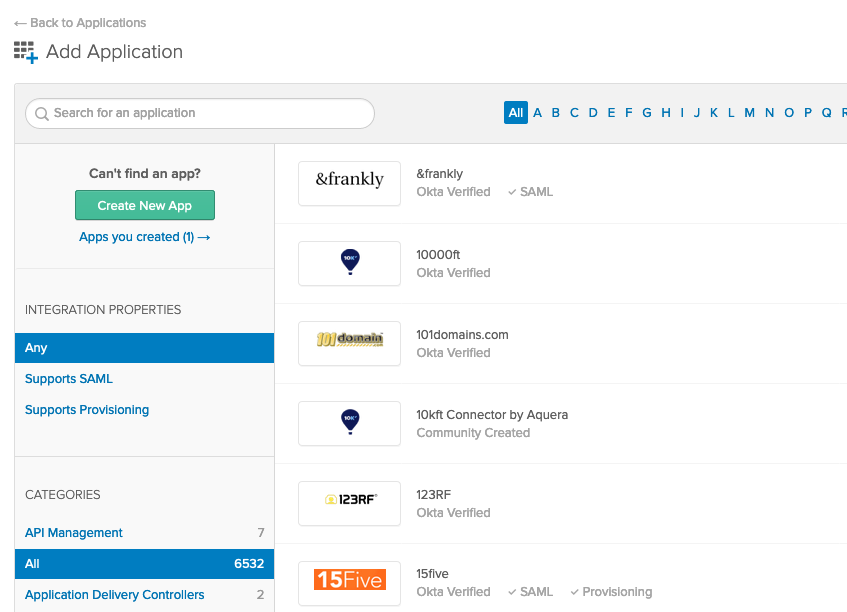
2. In the applications directory, click Create New App
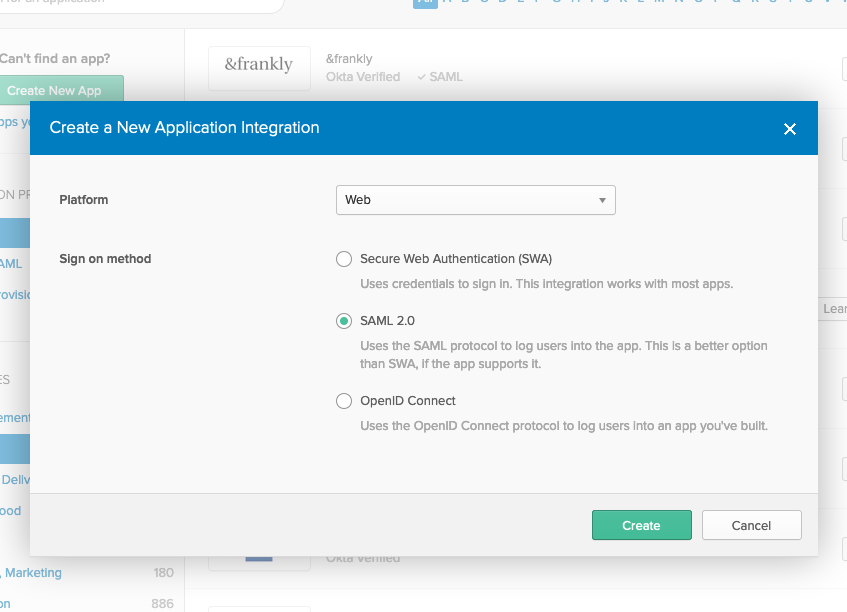
3. In the popup select Web from the dropdown and then select SAML 2.0
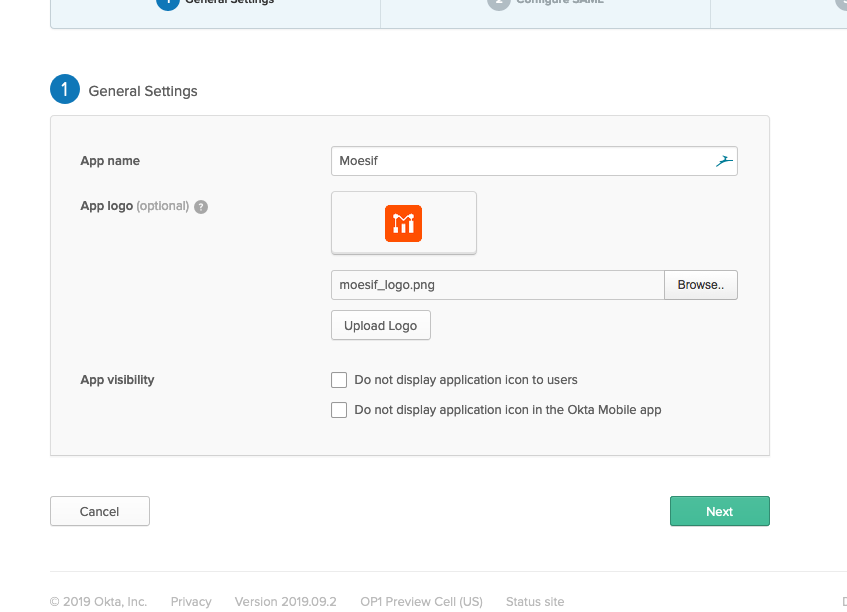
4. Enter a name for the app and optionally upload a logo
You can download the Moesif logo here
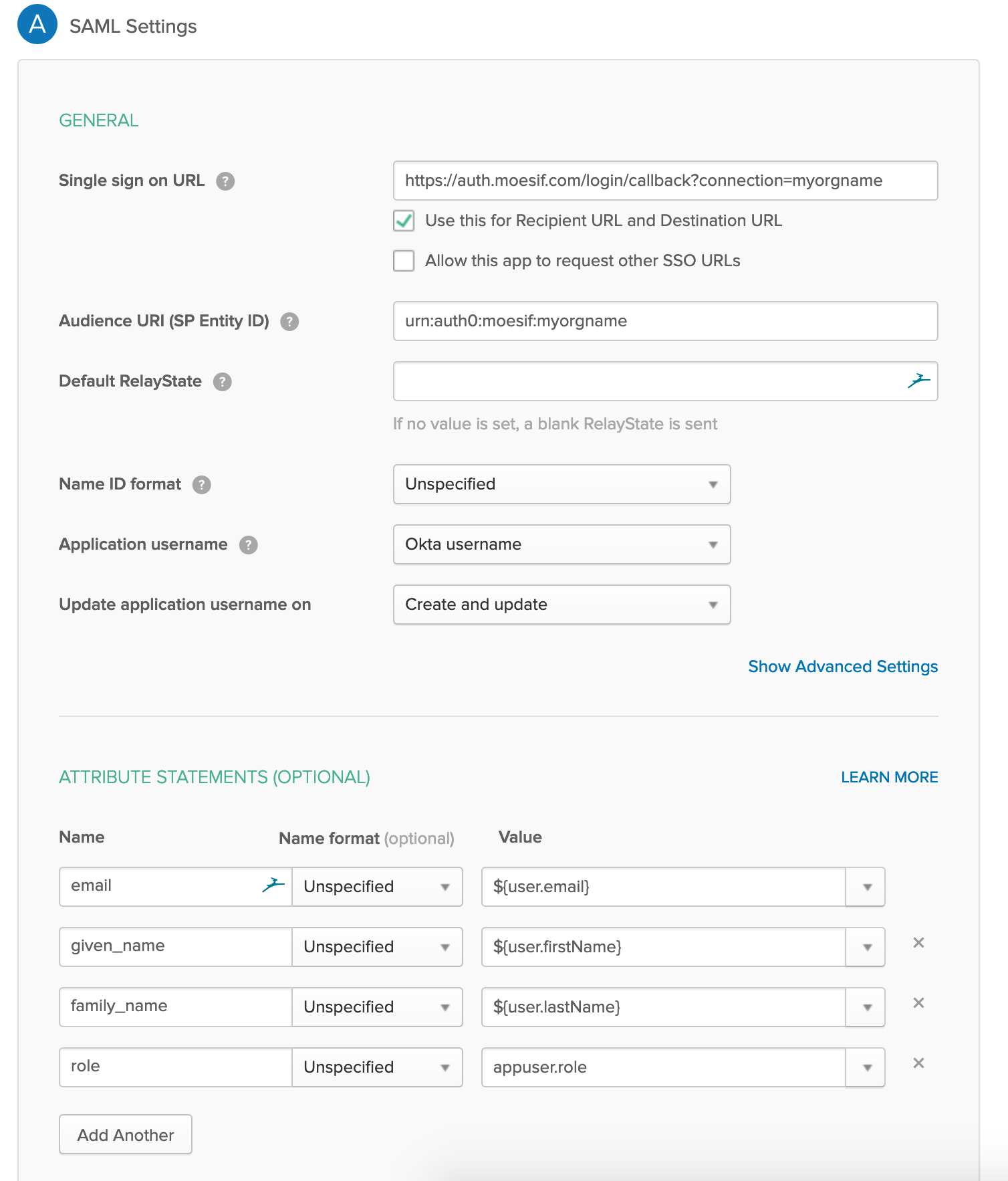
5. On the next step, enter your single sign on URL and Audience URI
The single sign on URL looks like https://auth.moesif.com/login/callback?connection=myorgname
The Audience URI looks like urn:auth0:moesif:myorgname
You can obtain your single sign on URL and Audience URI by emailing your Moesif technical account manager or support@moesif.com
Besides filling in the Single sign on URL and Audience URI fields, you will need to map four fields under Attribute Statements as specified below:
| Name | Name Format | Value |
|---|---|---|
| Unspecified | ${user.email} | |
| given_name | Unspecified | ${user.firstName} |
| family_name | Unspecified | ${user.lastName} |
| role | Unspecified | appuser.role |
All other fields can be left to their default values.
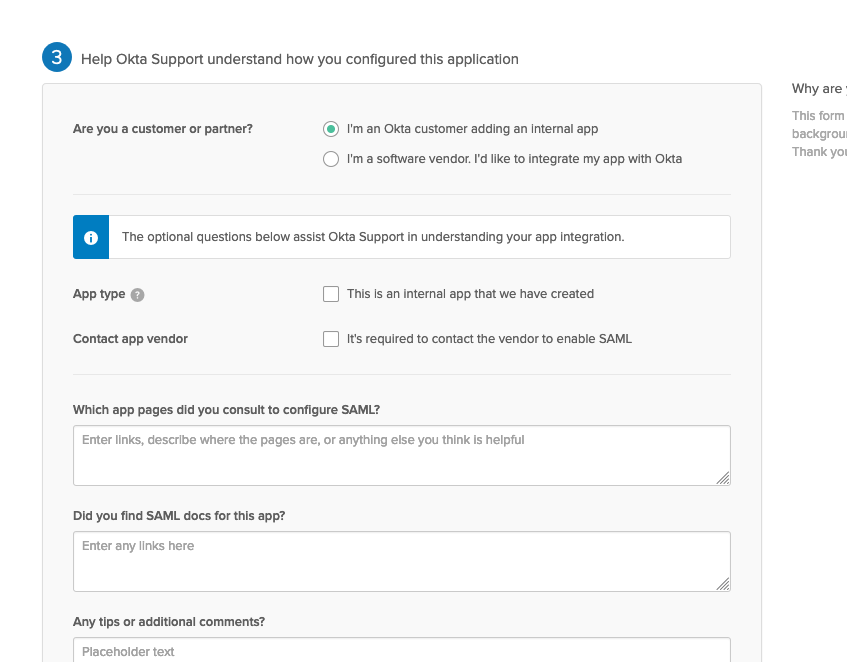
6. On the next step, select I’m an Okta customer adding an internal app and select finish
7. Finally, select View Setup Instructions in the yellow box
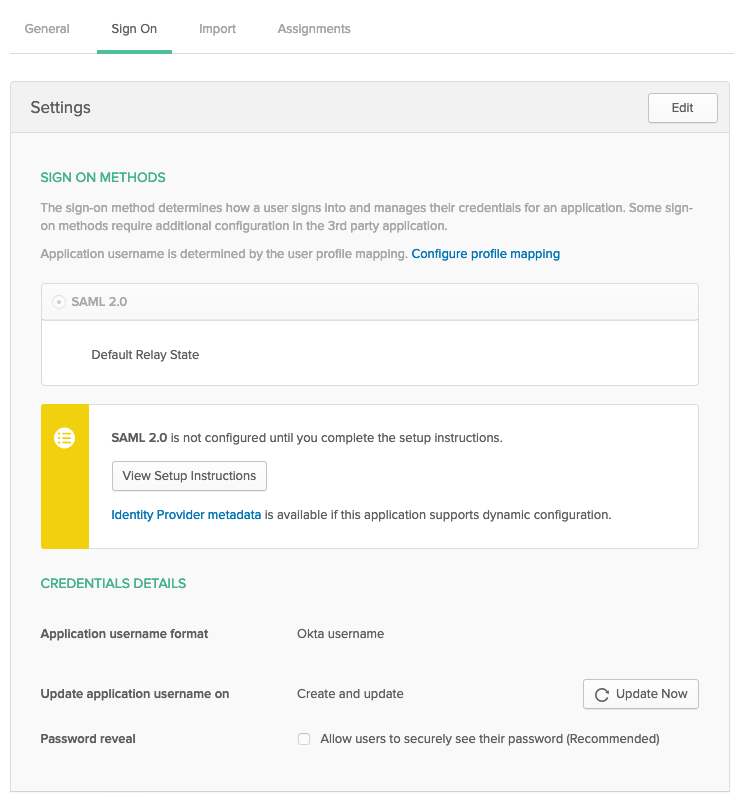
After clicking View Setup Instructions, you’ll see the Identity Provider Single Sign-On URL and your X.509 Certificate for the newly created application. Email both of these items to your Moesif technical account manager who will finalize linking your Moesif organization to your IdP application.
8. Add role field (Optional)
To manage role-based access control for Moesif within your identity provider, you can add a field role to the Moesif appuser.
Within the Okta admin portal, go to Directory -> Profile Editor, and select the Edit Profile button next to the newly created Moesif application.
Click on Add Attribute on the left side and add a field role as shown in below screenshot.
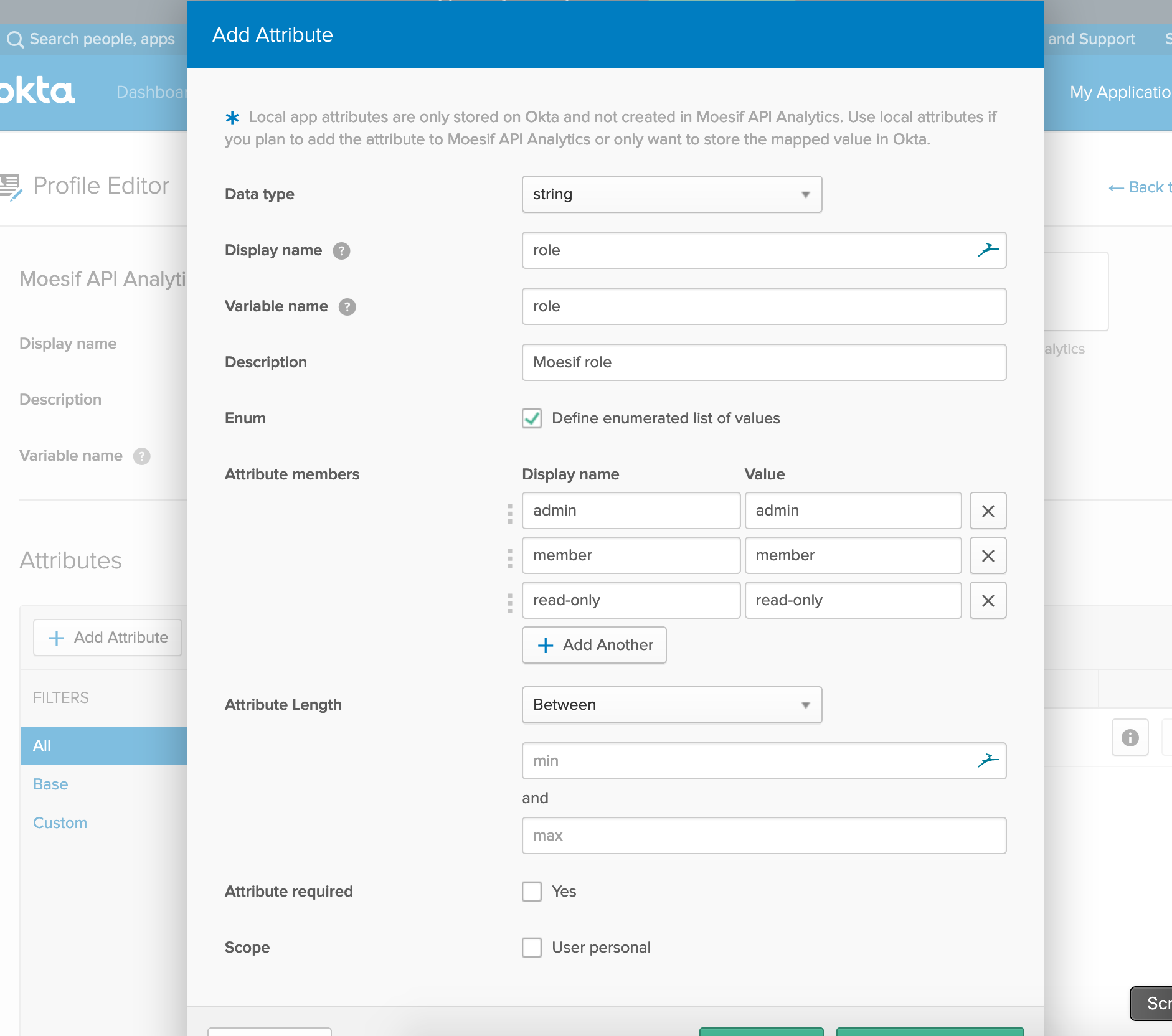
Checkbox Define enumerated list of values and add the three predefined roles supported by Moesif:
adminmemberread-onlydashboard-viewer
If your Moesif subscription has any custom roles, you can also add their names to this list.
After SSO activated
Once SSO is enabled:
- Team members will no longer be able to log in with a password or social account.
- Password reset is disabled.
- Administrators will no longer be able to add/remove team members within Moesif.
- Role-based access control is synced from your identity provider and cannot be changed within Moesif.
Any employee logging in with your company’s domain will automatically be redirected to the single sign-on page where they can click log in. All team management and role-based access control actions is done through your identity provider. Moesif automatically syncs user accounts.
Disabling SSO
An organization can disable SSO at any time by contacting their technical account manager. Once disabled, existing team members who already had an account prior to SSO can log in with their password. New users who were provisioned through SSO can reset their password to log in.